Personal data compliance has long been self-explanatory in its relevance. Meanwhile, the "heat" is increasing in one way or another. At the beginning of this year, draft laws on administrative and criminal liability for personal data leaks were adopted in the first reading, and organizations are awaiting the repeatedly announced introduction of turnover fines for leaks.

And while some are calmly waiting to see what requirements the legislative process will ultimately turn into, others are starting to prepare and conduct an audit of their personal data handling, while still others are protecting as they have always protected. At the InfoWatch Academy event with experts from "Kuper" (SberMarket) and MIEM NRU HSE, we will share methodological developments in personal data protection.
We will analyze what is important to do now, starting with the preparation of regulatory support and up to specific steps to be taken in building working and legally compliant procedures for personal data protection. We will announce a course on personal data protection developed by the InfoWatch Academy in collaboration with experts and speakers - relevant to everyone who needs to build compliance systems according to the new rules and successfully pass Roskomnadzor inspections.
- We will outline the key steps in building a personal data protection procedure in an organization. Where to start and what to pay attention to.
- We will review the list of internal regulations in organizing personal data protection. What documents are needed, for what purpose, and what the regulator will request during an inspection.
- What to do if an incident occurs and how a personal data operator should interact with Roskomnadzor in this regard.
- We will highlight errors in organizing protection and interacting with the regulator.
Today's event is led by Valentina Mironova, head of the personal data protection methodology group at Kuper.
Valentina Mironova proposed discussing aspects of the legislation that currently exist and are in effect. These are aspects related to the key steps in building a personal data protection system. We know that we have Federal Law No. 152 on personal data, and there are a number of requirements for protecting the data we process.
We will focus on the practical application of the current legislation.
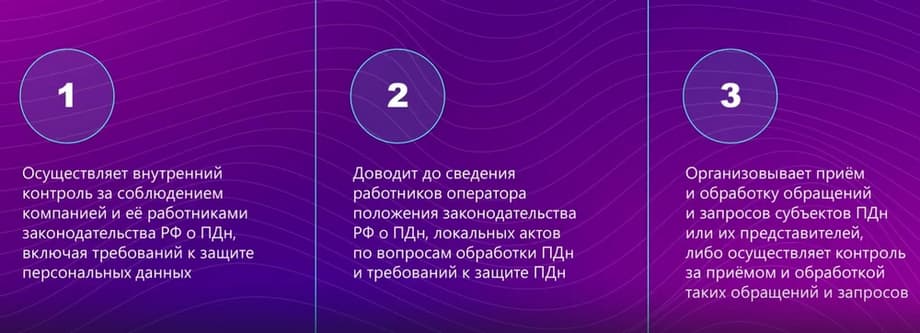
The first step to legally comply with the requirements is to appoint a responsible person according to the requirements of the law. This person is obliged to exercise internal control over compliance with the requirements of legislation in the field of personal data protection. And this specialist must regularly audit all existing data processing processes. They must inform the employees of the company in which they work of all provisions of the legislation in the field of personal data protection and their processing. There is another point that the person responsible for organizing processing must do. This is receiving appeals and requests from personal data subjects, as well as authorized bodies.
It should not be forgotten that all three of these responsibilities must be regulated by the company's internal regulatory documents.
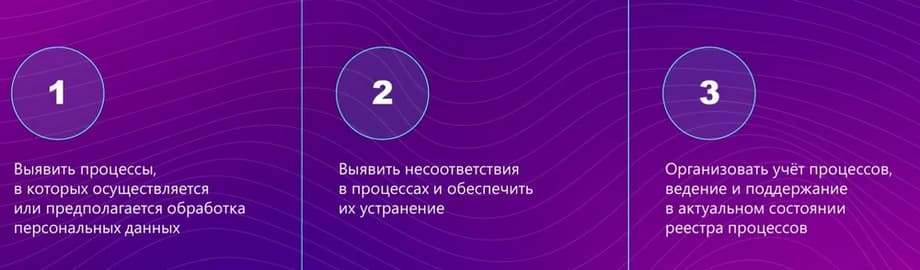
The next step that needs to be taken is to conduct an audit of personal data processing processes. You need to understand what personal data is processed in the company, in which business processes this personal data participates. We must definitely describe these processes and understand possible inconsistencies with the requirements of the law that currently exist. If there are any inconsistencies, they will certainly need to be addressed. Do not forget that all processes in which personal data is processed must be accounted for and, accordingly, their accounting, maintenance, and updating must be carried out, which means that not only should we audit the process in the second step and forget about it, but the processes should be living, that is, we must constantly audit them for possible changes that have occurred.
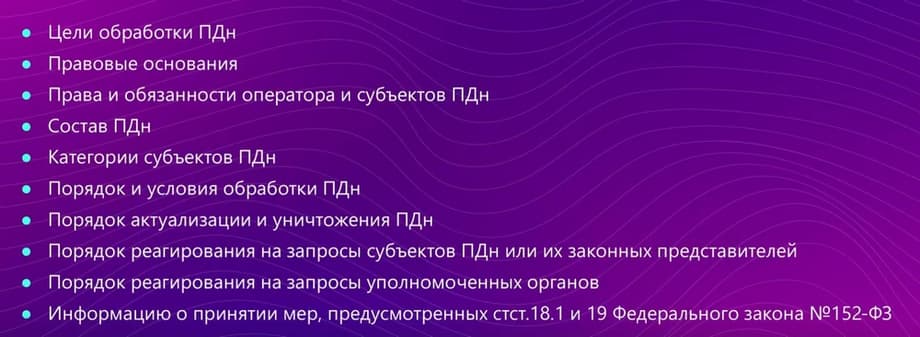
The next step, and one of the key ones, is the development of a policy regarding the processing of personal data. We are obliged to determine the purposes of processing, the legal grounds, the rights and obligations of the company as a personal data operator. We also determine the rights and obligations of personal data subjects, list the personal data that we process within the company. We determine the categories of subjects whose personal data is processed. And most importantly, the procedure and conditions for processing the data we have. That is, what we do with the data, how we process it, and so on. We determine the procedure for destroying this data, additions. That is, everything related to the articles of the federal law. We determine the procedure for responding to requests and the procedure for responding from authorized bodies. And of course, we do not forget about Article 18.1.19 of those requirements for security and measures that we are obliged to fulfill in relation to personal data. We do not forget that the policy on the processing of personal data is aimed at ensuring the legitimate rights and freedoms of personal data subjects.
It should not be forgotten that the development of a policy regarding the processing of personal data should be published in a generally accessible source, to which we must definitely refer.
We must definitely familiarize the same employees with the policy regarding processing. Another point related to the development of other provisions. We know that in addition to the policy regarding the processing of personal data, there must be a provision regarding the processing and protection of personal data. The procedure for storing and using employees' personal data must be determined.
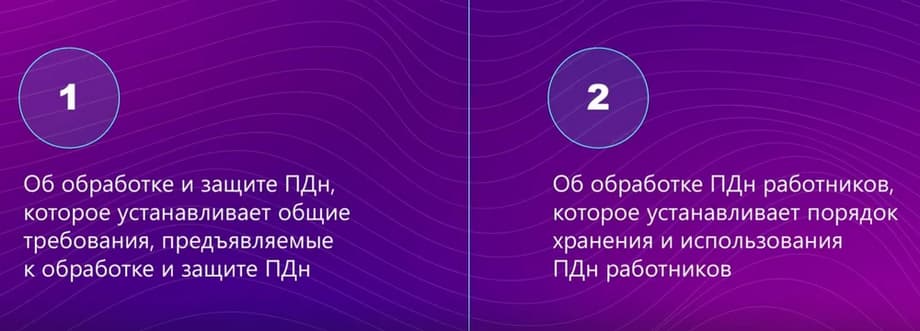
Some organizations have, in addition to automated processing, also non-automated processing of personal data, and, of course, the key document that regulates non-automated processing of personal data will be the provision regarding non-automated processing of personal data.
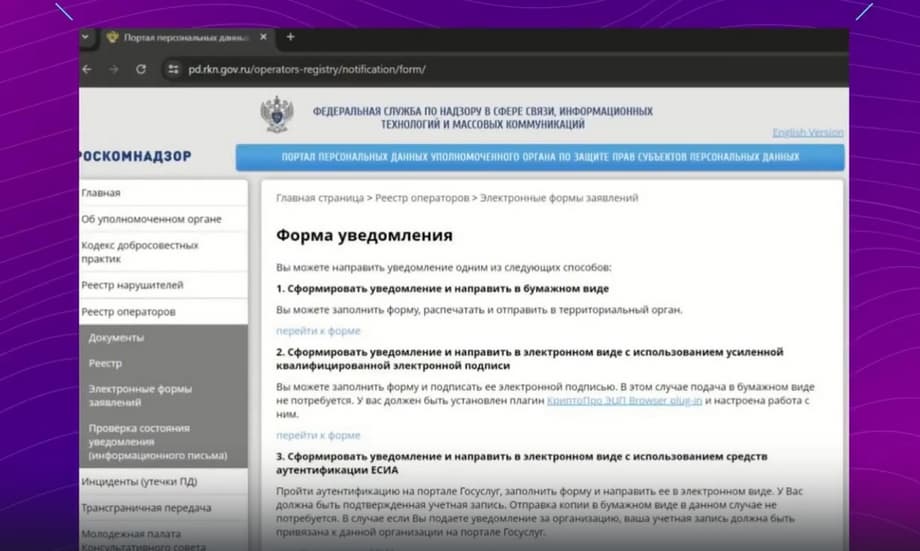
The next step, after we have determined the person responsible for working with personal data, we have developed our policy, we know everything, where, what is happening with us, we are obliged to submit notifications to Roskomnadzor.
Notifications to Roskomnadzor can be sent in two forms, in paper or electronic. If we are talking about paper form, then on paper with the signature of the general director of the company, we send it to the address of the territorial body. If we are talking about electronic form, we go to the Roskomnadzor website, fill in all the necessary fields and send notifications to Roskomnadzor. It should not be forgotten that after we have sent a notification to Roskomnadzor, there are cases if you have any changes as operators in relation to the processing of personal data, and these changes relate to the notification to Roskomnadzor, we are obliged to make appropriate corrections to the notification. You can also find out about this on the Roskomnadzor website. There is also such a point that in order to verify that you are a personal data operator and Roskomnadzor actually received your notification that you sent to it, you can use the register of operators and find your organization.
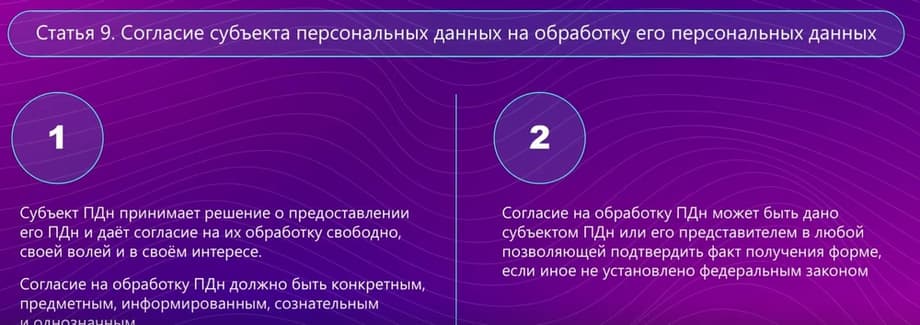
The next step is, of course, any action with personal data, well, in addition to those exceptions that are present in Article No. 9 of the federal law, they must be carried out with consent to the processing of personal data. We receive consent from personal data subjects.
And here, it is probably worth paying attention to the fact that the personal data subject decides to provide his personal data and gives consent to their processing according to his will. This is very important. Consent to processing must be specific, substantive, informed, conscious and unambiguous. In addition to who gives consent, to whom consent is given, a list of personal data, we also specify the methods of processing, the purposes for which consent is given, and necessarily the terms.
Of course, it should not be forgotten that there are two forms of consent. This is a simple form of consent and a written form of consent. If we are talking about a strictly established form of consent, then the data that should be in this form are present in Article 9, paragraph 2.
There is consent in a simple form. When, roughly speaking, we go to some site, set some checkboxes. But here it should not be forgotten that if we receive some consent, then we, as personal data operators, are obliged, in case it is necessary in the future, at the request of, for example, an authorized body or at the request of the subject himself, to confirm the fact of receiving such consent, we must definitely take this point into account. Here, the aspect that consent often changes is very important.
We are expanding our scope of activity, expanding the list of personal data. We must re-collect consents. Here I will draw attention to the fact that very many systems must store previously obtained consents when collecting consent. This is also very important, because when contacting Roskomnadzor, often in the request, there are questions related to some period, that is, the request is formulated as follows. Confirm the fact that you received consent from such and such a subject for the period, and it remains to add a specific period. We must specifically get this consent from the system and demonstrate it to the authorized body, give an answer that you actually received consent during this period of time, and it was like that. Maybe at the moment it is already different, but at that period it was exactly like that.
It is impossible to process personal data without consent. Well, I mean in those cases when it is necessary. Of course, there are other cases in the law when there is no need to obtain consent.
Let's move on to the next step. Assessing the potential harm that may be caused to personal data subjects. Order No. 178 on approval of requirements for assessing harm that may be caused to a personal data subject in case of violation of the requirements of the federal law was recently received. You are required to conduct an audit and assess the damage. A corresponding document must be drawn up here, this is an act, and it is mandatory. After we have assessed the damage from non-compliance with the requirements of Federal Law No. 152, we must move on to information systems for processing personal data.
Let me remind you that an information system for processing personal data is understood as a set of tools: there must be a database that we process, there must be software and hardware that process personal data. And it is from this paradigm that we proceed.
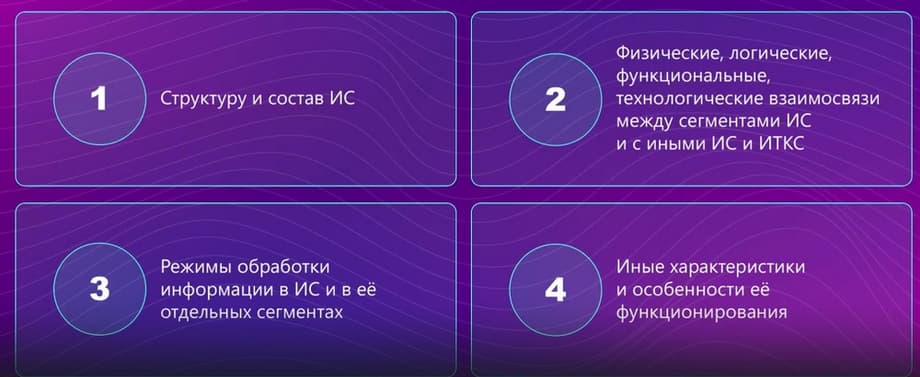
It is very important to conduct a survey of personal data information systems. We have audited the processes, we know what data, where it runs, why it runs, who is the user of this data, in which systems it is stored, but what are these systems? Of course, a survey of personal data information systems is certainly important because all threats and threat vulnerabilities come from the fact that we have a system. And the first fundamental step towards the presentation of any personal data protection system is this sequence. That is, we need to know what we will protect. We need to know the structure and composition of this information system, physical and logical connections, and other connections between the segments of the information system, between the TKS system itself, and possibly some other systems. That is, we must know, understand and describe the intricacies and nuances of the functioning of the information system.
We must understand the modes of personal data processing, who participates, what users there are, who belongs to the privileged and non-privileged, we must calculate the corresponding matrix for each information system, possibly some other characteristics of the system functioning, and so on. What personal data is in them, what data centers are used, how to create them.

Objects of protection. And for an information system of personal data, we understand everything by the object of protection. This includes information contained in the personal data information system, and technical means by which we process personal data, and software, and those information technologies that allow us to go into processing.
On February 5, 2021, the Federal Technical and Export Control Service of Russia approved the "Methodology for Assessing Information Security Threats."
If we return to the document I mentioned earlier, approved by the Federal Service for Technical and Export Control, it identifies the main ways to identify information security threats.
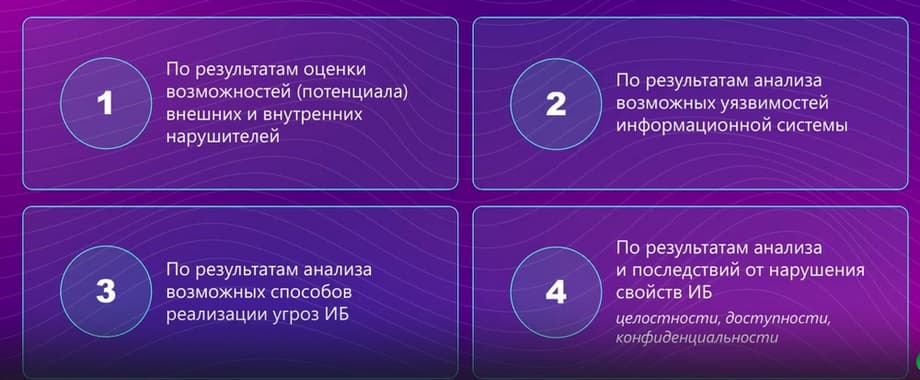
First of all, we remember that internal intruders are those intruders who are within the perimeter of your company, that is, inside the controlled area, and external intruders are those who are trying to get to you from the outside. We must assess, conduct an analysis of the vulnerability of the information system, as well as possible ways to implement threats, and, of course, assess the consequences that may occur when violating the properties of information security. I am talking about the three pillars that all "security guards" know. This is confidentiality, integrity and availability.
Threat assessment is carried out by an expert method, and often a commission of experts is assembled and a threat assessment is carried out. Do not forget that we have a threat data bank, the Federal Service for Technical and Export Control of Russia. That is, all the tools that are currently used must be applied in order to fully understand what threats are possible and what vulnerabilities are possible in the system. This will make it possible to create a more reliable information protection system than if we analyze a smaller number of sources.
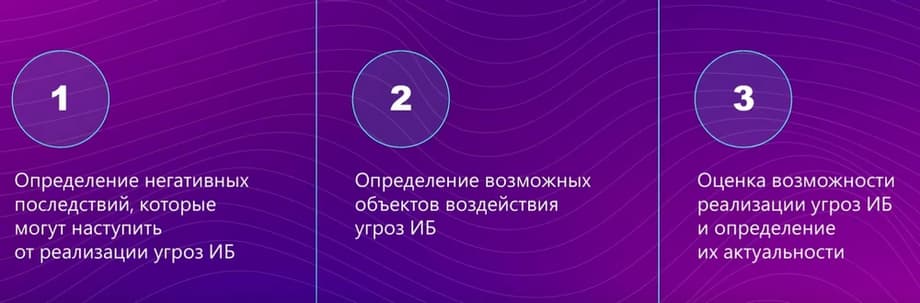
Stages of threat assessment. The first stage is to determine the negative consequences that may occur from the implementation of threats. Next, we determine the possible objects of threat impact, and, in fact, assess the possibility of threat implementation and its relevance. As initial data, as I said, use the BDU-stack of Russia in free access.
After we have built a model of threats and attackers, we have identified current threats, identified those attackers that are relevant to our specific system. Of course, part of the work on assessing security has already been completed. We know what personal data is present in the system, whose personal data, in what quantity.
But why is this step done after building a threat model, it is very important for us to know what type of threats are present in the system. We, I recall, have types of threats. The first type of threats are those threats that are associated with unauthorized access in system software. The second type of threats are those threats that are associated with unauthorized access in application software. And the third type of threats are not related to unauthorized access either in system or in application software.
Assessment of the security of personal data information systems is carried out on the basis of Government Decree No. 1119, which was issued in 2012. Here we identify the types of information systems, the types of threats, as well as the amount of information, those records about the subject of personal data that we have. And in accordance with this, we allocate 4 levels of security for each information system.
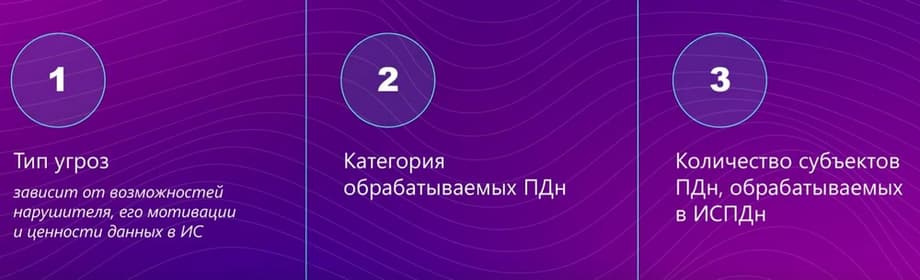
And accordingly, we draw up an act. Here is the type of threats, the category of personal data processing, the number of personal data subjects that are processed. After we have decided what we should protect ourselves from, that is, built a model of threats to the attacker, we now need to understand how we will protect ourselves. To do this, we create a technical task, a project of a personal data protection system, abbreviated as the SZPDn system.
There are three documents that will allow you to create a competent, correct system for the protection of personal data in relation to the legislation of the Russian Federation. We have order No. 17, which regulates the requirements for state information systems of personal data. There is order No. 21, which says what organizational and technical requirements must be met in relation to information systems of personal data. There is a difference between orders 17 and 21. It is significant, therefore, if we have a relationship with a state information system, there is a nuance here, which will be discussed later.
After we have developed technical specifications and a project for a personal data protection system, we need to purchase protection equipment, install it for configuration. Do not forget that the protection equipment must undergo an assessment procedure in accordance with the established procedure.
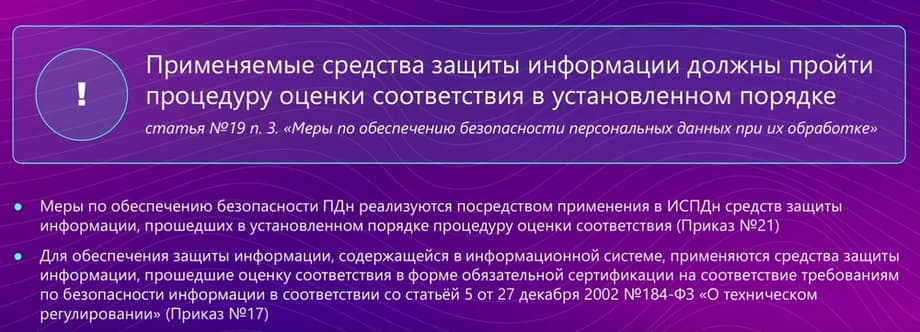
The same is said in order 21 and in order 17.
The next point is related to the evaluation of the effectiveness of the protective equipment used.
If we are talking about a regular information system, let's call it that - not a state information system, then the effectiveness assessment can be carried out by the operator independently or with the involvement of persons on a contractual basis. If we involve an organization to assess the effectiveness of the protective equipment used, then it is imperative that the colleagues have a license in accordance with the law. And the effectiveness assessment is carried out at least once every three years.
As for state information systems, the story is somewhat different, for state information systems, object certification is mandatory. After building a protection system, installing and configuring protection systems, they must undergo object certification.
We must constantly, in the process of creating a personal data protection system, draw up a number of internal regulatory documents (internal regulations). And if we create a protection system, it does not mean that we have created a protection system and forgotten about it. There must be constant control and monitoring of what is functioning.